Complete Guide to Salesforce Shield
Retaining field history for longer can allow you to adhere to business requirements (i.e. to refer back to historic data) or legal compliance requirements. Field Audit Trail allows you to track up to 60 fields per object in contrast to the 20 fields per object tracking that comes standard with Salesforce. Enabling Field Audit Trail after years of using standard field history tracking will not retroactively fill in the gaps. Shorter retention periods reduce storage overhead and improve query performance when accessing archived data. Tracking formula fields creates unnecessary performance overhead since their values derive from other tracked fields. Disable audit tracking on calculated fields unless regulatory requirements specifically mandate it.
Forensic Investigation Capabilities

Use a convenient UI to update data classifications as you discover and review fields containing sensitive data. Field Audit Trail lets you know the state and value of your data for any date at any time. You can use it for regulatory compliance, internal governance, audits, or customer service. Event Monitoring is like a window that shows all the granular details of user activity in your organization.
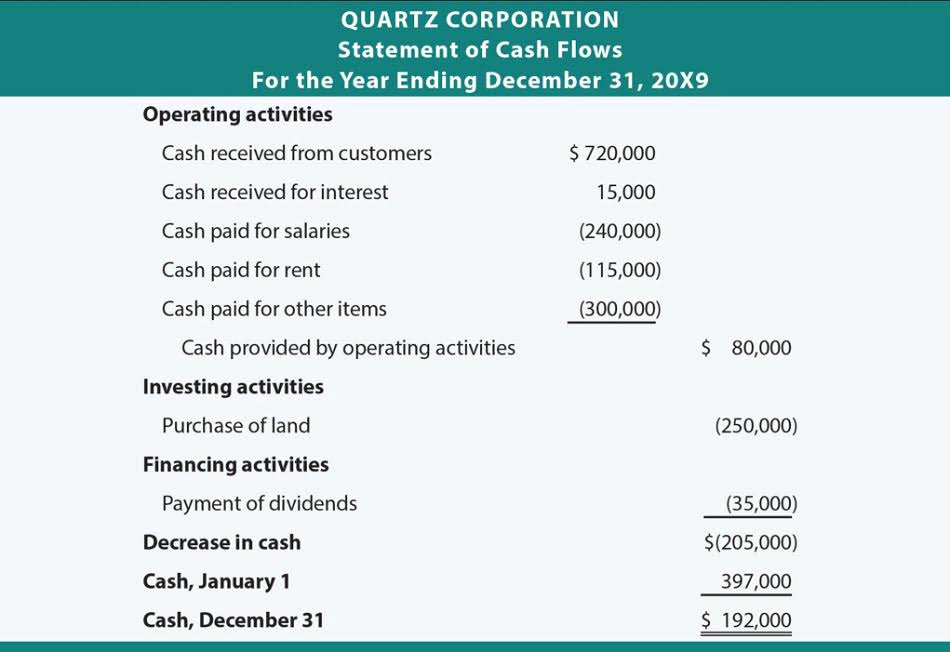
Services & Plans
- The Setup Audit Trail provides a broader view of changes made within the Salesforce org itself.
- Field Audit Trail lets you know the state and value of your data for any date at any time.
- Integrating Salesforce Shield with Reco’s SaaS Detection & Response solutions creates a powerful combination for enhancing your company’s security and compliance posture.
- Enabling Salesforce Field Audit Trail on objects with extensive field history can trigger large background jobs.
- Reporting snapshots, mass transfers and even using the Data Import Wizard are a few of the ones being captured.
- This is crucial for compliance, forensic analysis, and maintaining the integrity of critical business data.
This also proves that the audit trail can aid in troubleshooting certain situations. As cyber threats evolve, integrating advanced security measures like Salesforce Shield and maintaining a proactive security strategy are essential steps for any company. By doing so, businesses not only protect their critical data but also build a foundation of trust and compliance that supports long-term success.
Then, choose the Success Plan that’s right for your business.
In many cases, Salesforce products integrate directly with many outside applications and systems to help you connect your data. For those that don’t have built-in integration, like on-premises data sources, you can purchase licenses of MuleSoft, work with our integration partners, or use apps on AppExchange. With resources, guidance, and technical support, our three levels of Success Plans help your business get more value from Salesforce and prepare your Retained Earnings on Balance Sheet data for a future with AI.
Reco Security Experts
We really don’t want this, so we need to ensure that those values are being stored in the appropriate places. For reporting on Event Monitoring, Salesforce provides a CRM analytics app (pre-built dashboard), which comes with event monitoring (two licenses). There’s a robust set of events that Salesforce provides to monitor from a performance standpoint, for example, if certain reports are taking longer to load. Salesforce Shield is an add-on product, meaning it comes at an additional cost to the typical Salesforce CRM license types. It’s worth noting that you can purchase the “full umbrella” (all four components), or each component can be purchased separately based on what suits your regulatory and business requirements. Additionally, picklist value changes are going to be displayed individually for added clarity when analyzing these in particular.
Can I upgrade at anytime? Can I add more products later on?
- These, alongside the org-wide defaults, are changes that are also available for review.
- No matter how you choose to manage your keys, Shield Platform Encryption secures your key material at every stage of the encryption process.
- User activity monitoring allows you to set transaction security policies to track user “events,” i.e. what they are doing in the system, through browsers, the Salesforce mobile app, and the Salesforce APIs.
- I find that taking note of the whole name “Setup Audit Trail” makes it easier to remember that this tracks changes made “within Setup”, which is quite a contrast compared to Field History Tracking.
- The good news is that you don’t have to enable it, but users who need access to this section need the View Setup and Configuration permission.
- Depending on your unique business needs, engaging with either or both can maximize your ROI.
- On the next screen, you’ll see a list of Objects and their related Standard Fields that you can encrypt.
On the next screen, you’ll see a list of Objects and their related Standard Fields Accounting Periods and Methods that you can encrypt. Click the Edit button and select which ones you’d like covered by Shield Platform Encryption. Think of your secret like a password – it is good practice to change it relatively frequently.
The Setup Audit Trail provides a broader view of changes made within the Salesforce org itself. I find that taking note of the whole name “Setup Audit Trail” makes it easier to remember that this tracks changes made “within Setup”, which is quite a contrast compared to Field History Tracking. Large organizations can align Shield configurations to their regulatory control matrix. Ultimately, these aren’t necessarily big gaps, but if your auditors want to see them, you’ll need to rely on something other than the Setup Audit Trail. Stay ahead of identity-based threats — proactively remediate risks, block attacks, and ensure rapid recovery. Secure endpoints and audit trail prevent data loss while keeping teams productive — no matter where they work.